Nist Cybersecurity Framework Policy Template Guide
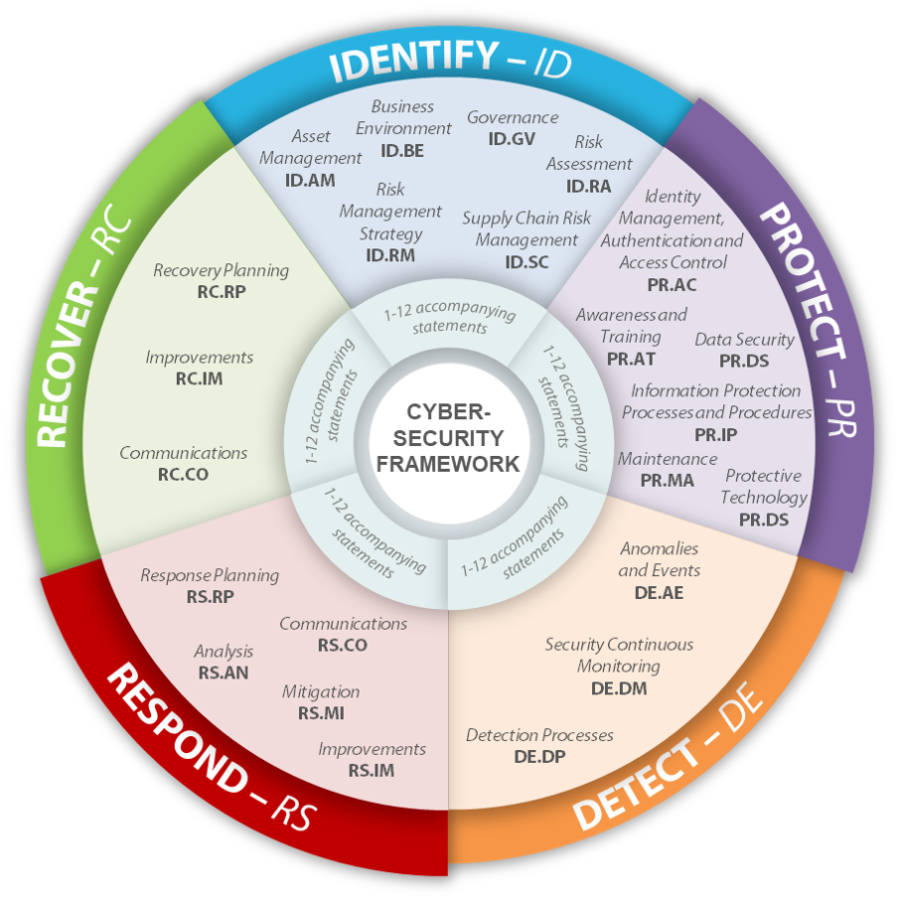
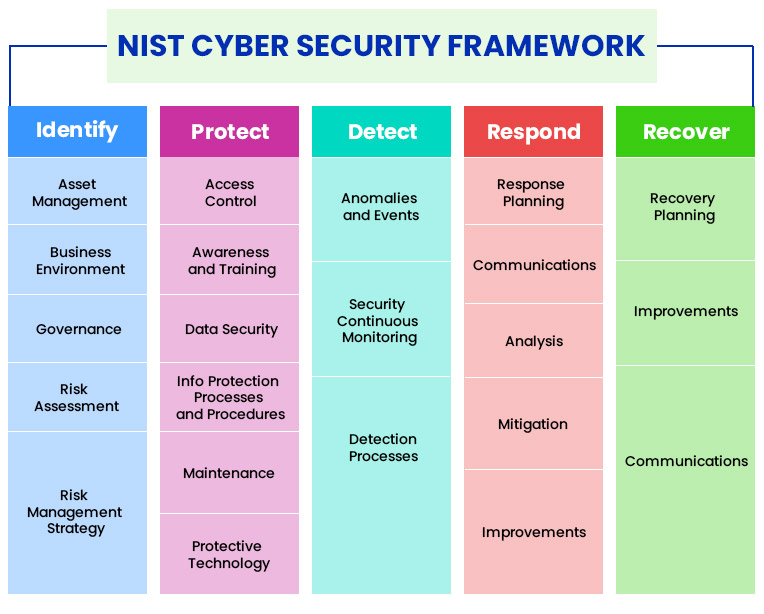
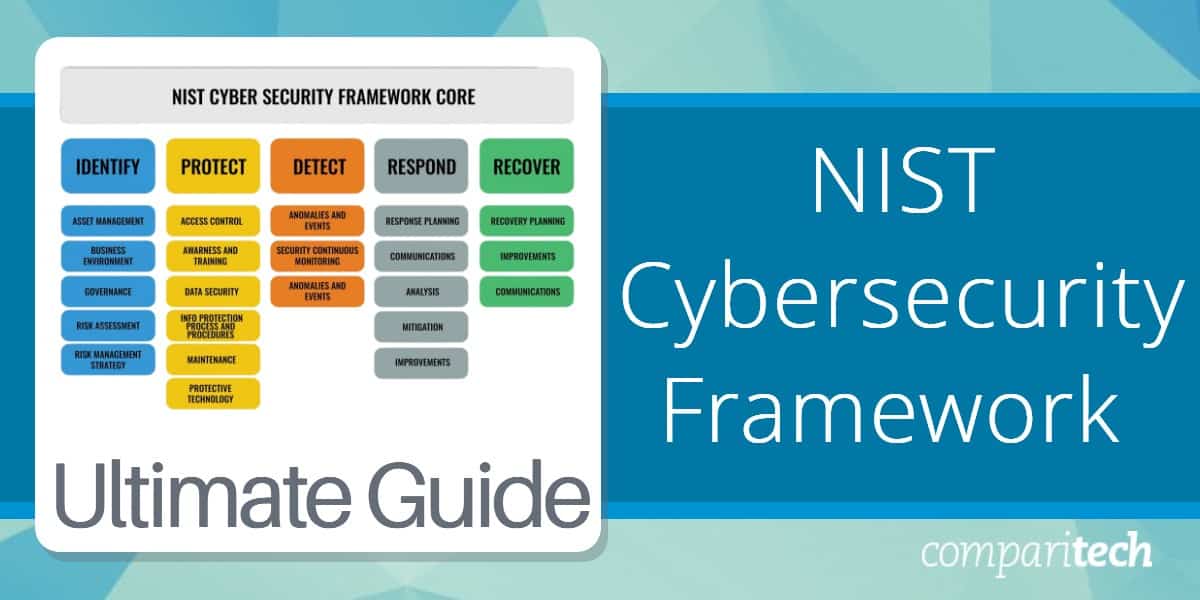
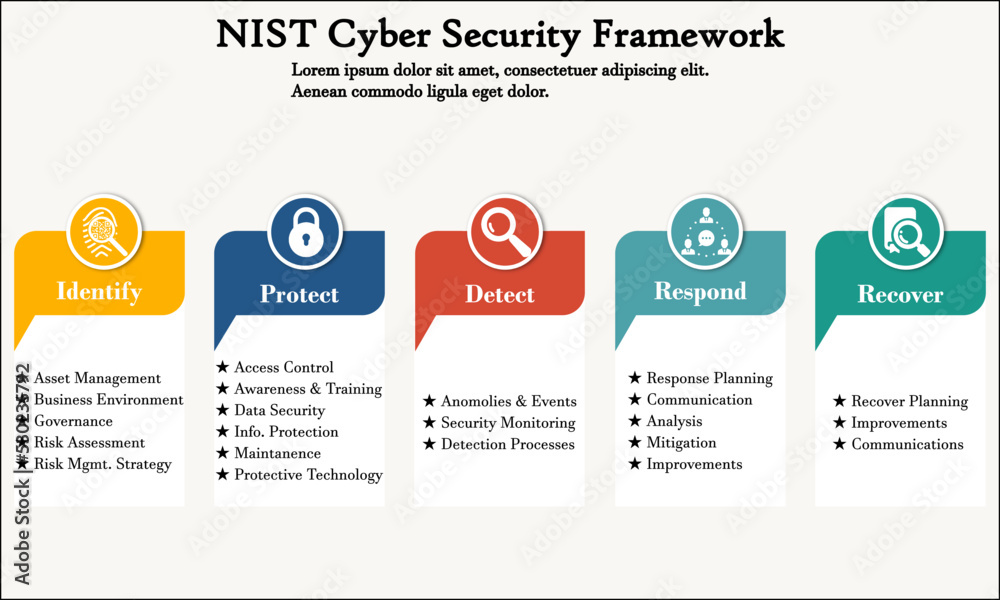
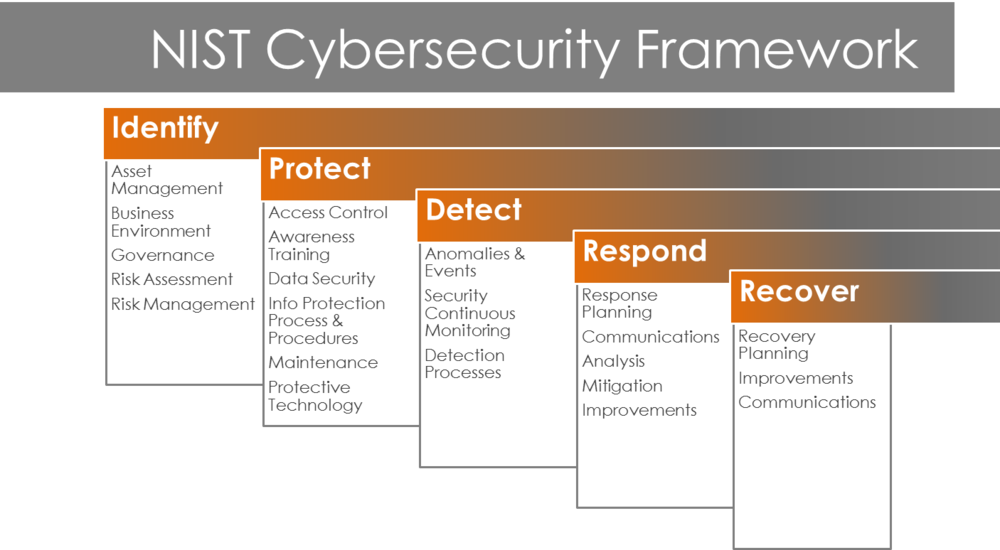
Nist Cybersecurity Framework Policy Template Guide - Learn how heimdal® can help you implement and manage. For industry, government, and organizations to reduce cybersecurity risks. This article delves into the components of the nist cybersecurity framework, outlines the importance of a policy template, and offers a comprehensive guide on drafting an. What is the csf 2.0.and popular ways to use it? Csf 2.0 resource center expand or collapse. Cyber security policies can focus on various aspects of an organization’s security profile. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. View the quick start guides. Download (pdf) quick start guides; Approaches, methodologies, implementation guides, mappings to the framework, case studies, educational materials,. Learn how heimdal® can help you implement and manage. Staying compliant should be a bonus to. Ransomware is a type of malicious attack where attackers encrypt an organization’s data and demand payment to restore access. Attackers may also steal an. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. Download (pdf) quick start guides; The nist cybersecurity framework (csf) 2.0 provides guidance to industry, government agencies, and other organizations to manage cybersecurity risks. For industry, government, and organizations to reduce cybersecurity risks. Different organizations can select from. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. Staying compliant should be a bonus to. Ransomware is a type of malicious attack where attackers encrypt an organization’s data and demand payment to restore access. The cybersecurity framework (csf) 2.0 is designed to help organizations of all sizes and sectors — including industry, government, academia, and nonprofit — to manage and reduce their. This guide gives the correlation between. View the quick start guides. What is the csf 2.0.and popular ways to use it? Cyber security policies can focus on various aspects of an organization’s security profile. Resources include, but are not limited to: This article delves into the components of the nist cybersecurity framework, outlines the importance of a policy template, and offers a comprehensive guide on drafting. The nist cybersecurity framework (csf) 2.0 can help organizations manage and reduce their cybersecurity risks as. Resources include, but are not limited to: Approaches, methodologies, implementation guides, mappings to the framework, case studies, educational materials,. The nist cybersecurity framework (csf) 2.0 provides guidance to industry, government agencies, and other organizations to manage cybersecurity risks. The nist cybersecurity framework 1 is. View the quick start guides. Resources include, but are not limited to: Download free and customizable templates to assess your compliance with the nist cybersecurity framework. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. What is the nist cybersecurity framework, and how can my organization use it? This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. For users with specific common goals. Line of effort 1.3.3 to promote the development of international. In furthering the national cyber workforce and education strategy, this. What is the nist cybersecurity framework, and how can my organization use it? Ransomware is a type of malicious attack where attackers encrypt an organization’s data and demand payment to restore access. Different organizations can select from. In furthering the national cyber workforce and education strategy, this environmental scan supports:. Line of effort 1.3.3 to promote the development of international. This article delves into the components of the nist cybersecurity framework, outlines the importance of a policy template, and offers a comprehensive guide on drafting an. Line of effort 1.3.3 to promote the development of international. Approaches, methodologies, implementation guides, mappings to the framework, case studies, educational materials,. This cybersecurity framework (csf) 2.0 community profile identifies 74 the security objectives. Staying compliant should be a bonus to. View the quick start guides. Download free and customizable templates to assess your compliance with the nist cybersecurity framework. Ransomware is a type of malicious attack where attackers encrypt an organization’s data and demand payment to restore access. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans. The nist cybersecurity framework (csf) 2.0 provides guidance to industry, government agencies, and other organizations to manage cybersecurity risks. Line of effort 1.3.3 to promote the development of international. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. Learn how heimdal® can help you implement and manage. For industry, government, and. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. Attackers may also steal an. This cybersecurity framework (csf) 2.0 community profile identifies 74 the security objectives from the nist csf 2.0 that support governing management of, 75 identifying, protecting. Ransomware is a type of malicious attack where attackers encrypt an organization’s data and. The nist cybersecurity framework (csf) 2.0 provides guidance to industry, government agencies, and other organizations to manage cybersecurity risks. What is the nist cybersecurity framework, and how can my organization use it? Ransomware is a type of malicious attack where attackers encrypt an organization’s data and demand payment to restore access. In furthering the national cyber workforce and education strategy, this environmental scan supports:. This cybersecurity framework (csf) 2.0 community profile identifies 74 the security objectives from the nist csf 2.0 that support governing management of, 75 identifying, protecting. This guide gives the correlation between 49 of the nist csf subcategories, and applicable policy and standard templates. What is the csf 2.0.and popular ways to use it? For users with specific common goals. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. View the quick start guides. The nist cybersecurity framework 1 is voluntary guidance, based on existing standards, guidelines,. Download free and customizable templates to assess your compliance with the nist cybersecurity framework. Organizations use a cybersecurity framework as a structured system of guidelines and best practices to manage their cybersecurity risks. This guide gives the correlation between 35 of the nist csf subcategories, and applicable sans policy. The nist cybersecurity framework provides essential guidelines to help you manage risks and protect sensitive data effectively. Staying compliant should be a bonus to.SOLUTION Nist cybersecurity framework policy template guide
NIST Cybersecurity Framework Guide Technology Comparison
Policy Template Guide NIST Cybersecurity Framework PDF Security
Nist Cybersecurity Framework Policy Templates
Nist Cybersecurity Framework Policy Template Guide
Nist Cybersecurity Framework Policy Template Guide
Nist Cybersecurity Framework Policy Template Guide
Nist Cybersecurity Framework Policy Template Guide
NIST Cyber Security framework with icons in an infographic template
Nist Security Plan Template
Download (Pdf) Quick Start Guides;
The Nist Cybersecurity Framework (Csf) 2.0 Can Help Organizations Manage And Reduce Their Cybersecurity Risks As.
Learn How Heimdal® Can Help You Implement And Manage.
Approaches, Methodologies, Implementation Guides, Mappings To The Framework, Case Studies, Educational Materials,.
Related Post: